
INFERMAL Project: Analyzing Features of Malicious Domain Registrations
Oct 24, 2024 · Yevheniya Nosyk, Maciej Korczyński, Carlos Gañán, Sourena Maroofi, Jan Bayer, Zul Odgerel, Samaneh Tajalizadehkhoob, Andrzej Duda
INFERMAL Project, funded by ICANN and conducted by KOR Labs, is dedicated to understanding the selection patterns behind cybercriminals' preferences for specific domain name registrars and top-level domains (TLDs) in their phishing operations. Our goal is to dissect the factors that make certain registrars and TLDs particularly attractive to attackers.
Read more
Building a Resilient Domain Whitelist to Enhance Phishing Blocklist Accuracy
Sep 8, 2024 · Jan Bayer, Sourena Maroofi, Andrzej Duda, Yevheniya Nosyk, and Maciej Korczyński
Community-driven and automated methods for constructing phishing blocklists may occasionally result in false positives, erroneously flagging benign domains or URLs as malicious. This blog discusses how we address this problem.
Read more
The D(M)ARC Side of the Email Reporting System
Aug 15, 2024 · Olivier Hureau, Jan Bayer, Andrzej Duda, and Maciej Korczyński
This blog post presents a large-scale study of DMARC to observe the user habits and preferences, consider the evolution of DMARC adoption in time, and understand how popular domains use DMARC.
Read more
Phishing Attack Trends
Jul 30, 2024 · Rowena Schoo, Maciej Korczyński, and Zul Odgerel
Since collecting and publishing data on the number of unique domains used for phishing attacks and malware distribution as part of our NetBeacon MAP reporting, we've been on the lookout for any discernible patterns or trends. This blog post discusses one of those.
Read more
Measuring DNS Abuse is Difficult
Feb 29, 2024 · Rowena Schoo
This blog is a condensed overview from our full report titled "Why do different DNS Abuse measurement projects result in different numbers" and is meant to create a greater awareness of how DNS Abuse is measured and help the community to understand and interrogate data presented to them.
Read more
Challenges in Measuring DNS Abuse
Nov 2, 2023 · Rowena Schoo and Maciej Korczyński
This blog covers an interesting case of suspected abuse in a gTLD registry between February and April 2023. It is a good example of an edge case, where the decision on whether or not to mitigate was not clear cut, and different levels of evidence were available at different time.
Read more
Introducing Compass Dashboards
Oct 24, 2023 · Rowena Schoo
Compass Dashboards empower registries and registrars with data to understand phishing and malware trends in their zone, over time, and compared against peers.
Read more
INFERMAL: Investigating Cyber Attackers' Preferences in Domain Registrations for Enhanced Online Security
Oct 2, 2023 · Maciej Korczyński and Samaneh Tajalizadehkhoob
The goal of the INFERMAL project is to conduct an in-depth analysis of maliciously registered domain names, aiming to uncover cyber attackers' preferences and possible measures to mitigate abusive activities within the domain name space.
Read more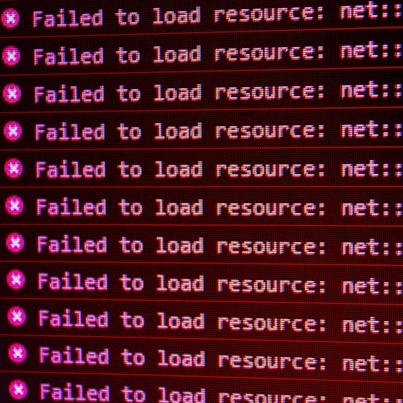
Extended DNS Errors: Unlocking the Full Potential of DNS Troubleshooting
Sept 28, 2023 · Yevheniya Nosyk, Maciej Korczyński, and Andrzej Duda
The Domain Name System (DNS) has traditionally relied on response codes to signal anomalies, but they are of little help to precisely identify the root causes behind failures. In this article, we examine the new Extended DNS Errors (EDE) mechanism that provides extra feedback on DNS resolutions.
Read more
A New Phase of Measuring DNS Abuse
June 8, 2023 · Rowena Schoo
Today the DNS Abuse Institute ("DNSAI" or the "Institute") adds a new level of reporting for our measurement project: DNSAI Compass™ ("Compass"). With his new level of reporting we intend to show the spectrum of how malicious phishing and malware is distributed across the DNS registration ecosystem.
Read more
SAV: Why Is Source Address Validation Still a Problem?
May 2, 2023 · Qasim Lone, Yevheniya Nosyk, and Maciej Korczyński
Despite being a known vulnerability for at least 25 years, source IP address spoofing remains a popular attack method for redirection, amplification, and anonymity. In this post, we provide an introduction / refresher on what SAV is and discuss methods to detect non-compliant networks and the incentives that the industry must enact to make the deployment of SAV attractive.
Read more
New ICANN Project Explores the Drivers of Malicious Domain Name Registrations
Apr 25, 2023 · Maciej Korczyński and Samaneh Tajalizadehkhoob
ICANN is funding a new project that aims to systematically analyze the preferences of cyberattackers and possible measures to mitigate malicious activities across top-level domains (TLDs).
Read more
Intercept and Inject: DNS Response Manipulation in the Wild
April 7, 2023 · Yevheniya Nosyk, Qasim Lone, Yury Zhauniarovich, Carlos H. Gañán, Emile Aben, Giovane Moura, Samaneh Tajalizadehkhoob, Andrzej Duda, and Maciej Korczyński
In November 2021, Internet users from Mexico lost access to whatsapp.net and facebook.com. Here, we present key takeaways from our analysis of the event - carried out with RIPE Atlas - and we look at the extent to which queries to DNS root servers get manipulated.
Measuring DNS Abuse: Our first report
Sep 16, 2022 · Rowena Schoo, Graeme Bunton, and Maciej Korczyński
In May 2022, we wrote about kicking off our work to measure DNS Abuse. We are proud to announce today that we have launched our first report and gone live with our measurement initiative: DNSAI Intelligence.
Read more
Are you filtering for inbound spoofed packets? Chances are you're not
Feb 15, 2021 · Yevheniya Nosyk, Maciej Korczyński, Qasim Lone, Marcin Skwarek, Baptiste Jonglez, and Andrzej Duda
Source Address Validation (SAV) is the best current practice (BCP 38 / RFC 2827) aimed at filtering packets based on source IP addresses at the network edge. In this article, we show how to identify networks that do not deploy SAV for incoming traffic.
Read more